Loading
This event has given rise to heated debate and controversy regarding the right to a private life and the legality of the method used to break into the phone, reminding us that telephones and tablets, which are becoming more and more common as part of IT solutions, are becoming an increasingly sensitive element in terms of information security.
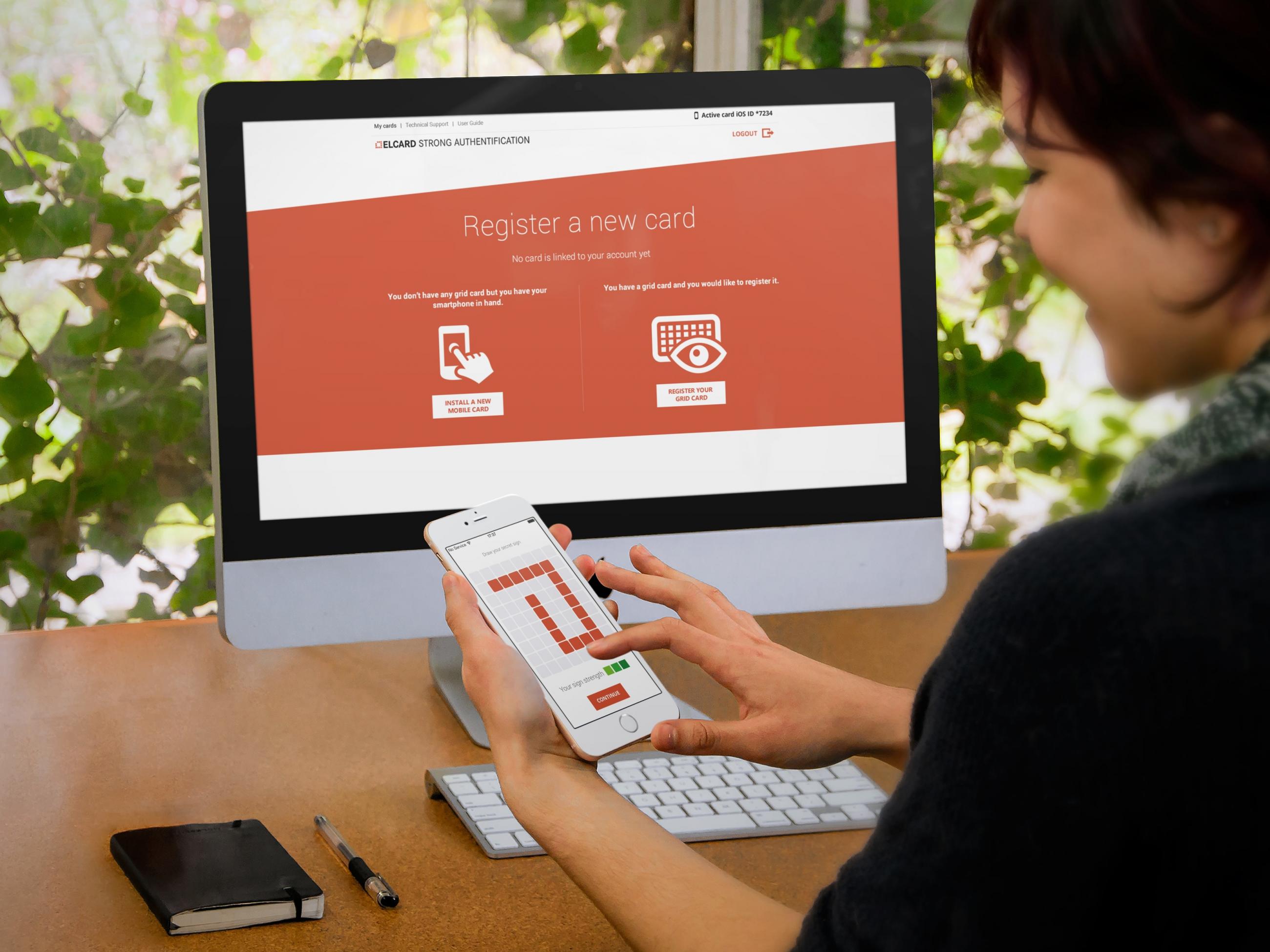
Security specialists are on the case, working to protect companies’ data against external attacks and are constantly adapting the systems used to ensure maximum protection for their information. On the other hand, as employees, we are also demanding easier access to this data in mobile environments, even in situations where the connection is sub-optimal. Users can therefore carry sensitive data in their pockets, and in so doing, run the risk of having their devices stolen by third parties – or simply misplacing them. Protecting data on mobile applications is therefore very important. While it is a little technical, we explain what you can do to secure your data.
Risks specific to mobile devices
The current trend of using private devices in a professional setting (bring your own device - BYOD) further complicates this problem by allowing business applications (with company data) to run alongside applications for private use (such as games). Such private applications may not always come from reliable sources, and the applications may be able to interact with the mobile device without this necessarily being visible to the user. An application such as Facebook running on an Android platform, for example, is notified when an SMS is received, and can even intervene further (by reading the SMS, saving the information it contains, or sending the SMS to another application).
This is a critical issue, because some e-banking systems use a secure authentication system based on SMS messages, and there is nothing in place to ensure that these messages are not intercepted by an application such as Facebook, or even transferred and stored in the foreign application’s database. Something that is possible with Facebook is also possible with a malicious application, distributed under the guise of a free game, for example. Once permissions have been granted, the application can access a range of information from a smartphone. It is worth mentioning that the new version of Android (version 6) allows individualized permissions management as is possible on iOS, but there is nothing in place to force applications to adhere to this new method of authorization (mainly due to the need to ensure backward compatibility).
Juan Avellan
General Manager Senthorus
Introducing Juan Avellan, our SOC Expert